10 tips for using Google+
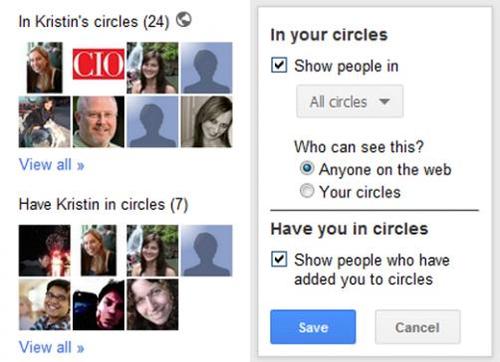
You just got your hands on a Google+ invite, but what next? Check out these ideas to get started using Google's new social network.
27 Jul | View galleries

The virtual world is full dangers lurking at every corner. You may never know when someone hacks into your device, online accounts, computer, etc. Most internet users – especially Aussies – believe they won’t ever fall victim to cyber-crime. However, they are sadly mistaken. Don’t wait until you become a victim. Instead, be proactive and take the required measures to protect your online privacy and financial transactions. Here are some ways to protect yourself from hackers and third-party agencies.

A bug in the Chrome browser caused security errors to be shown to users when trying to access HTTPS-enabled websites using Symantec SSL certificates.
Lucian Constantin | 06 Dec | Read more
Researchers from Northwestern University discover how an attacker could write a Firefox add-on that takes advantage of security holes in other Firefox add-ons to do its bidding.
Nick Mediati | 11 Apr | Read more
Reddit has removed a notice, known as a warrant canary, from its transparency report for 2015, suggesting that it may have received a secret national security order for user data.
John Ribeiro | 01 Apr | Read more

The U.S. Federal Communications Commission has taken a major step toward new regulations requiring Internet service providers to get customer permission before using or sharing their Web-surfing history and most other personal information.
Grant Gross | 01 Apr | Read more

A few weeks back, after the Working Mac column about scanning your Mac for viruses I received an email message from Yolanda:
Jeffery Battersby | 26 Jun | Read more
Google recently added another option to its Takeout service that lets you export data from your Google account, and the latest addition is one of the most important: Your Google search history.
The Internet of Things is based on sensors and controls in all sorts of devices. When those types of devices are used to create a smart home, they can give residents unprecedented control and insight. The proliferation of smart devices, however, also opens the door to new dangers and threats.
Jake Widman | 10 Mar | Read more
In our last episode of Private I, I explained the basics of public-key (PK) cryptography, a way to scramble messages in a way that only someone possessing a particular key can decrypt, without that key ever having to be publicly disclosed or shared. It's an effective system that has no known theoretical exploits, and currently deployed implementations are considered robust.
Glenn Fleishman | 02 Mar | Read more
The number of personal cloud users increases every year and is not about to slow down. Back in 2012 Gartner predicted the complete shift from offline PC work to mostly on-cloud by 2014. And it's happening.
Victoria Ivey | 16 Dec | Read more
Patrick Heim is the (relatively) new head of Trust & Security at Dropbox. Formerly Chief Trust Officer at Salesforce, he has served as CISO at Kaiser Permanente and McKesson Corporation. Heim has worked more than 20 years in the information security field. Heim discusses security and privacy in the arena of consumerized cloud-based tools like those that employees select for business use.
David Geer | 07 Aug | Read more
A few weeks ago, I got two fat envelopes in the mail. Each one held a new credit card inside along with instructions on how to use that card. Then, when I stopped at my local grocery store, at Nordstrom, even the corner liquor store, each had a new reader with a slot at the bottom into which I could slide those new cards.
Jen A. Miller | 11 Jun | Read more
This vendor-written tech primer has been edited by Network World to eliminate product promotion, but readers should note it will likely favor the submitter's approach.
By Steve Martino, Vice President, Chief Information Security Officer, Cisco | 23 Apr | Read more
Almost 1-in-5 (18-per cent) of businesses experienced a distributed denial-of-service attack within a year-long timeframe, according to the Global IT Security Risks Survey 2014 - Distributed Denial of Service (DDoS) Attacks from Kaspersky Labs and B2B International.
David Geer | 07 Apr | Read more
When it comes to cybersecurity, people are the biggest problem. Or, you could make that "problems."
Taylor Armerding | 17 Mar | Read more

This quarter’s report includes data gathered from across the Akamai Intelligent Platform during the third quarter of 2014. This report covers: •Attack traffic and Internet connection speeds/broadband adoption across both fixed and mobile networks •Insight into several high-profile security vulnerabilities, attacks, and toolkits, the state of IPv4 exhaustion and IPv6 adoption, Internet disruptions that occurred during the quarter •And, observations from Akamai partner Ericsson regarding data and voice traffic growth on mobile networks


